One-Click DNSmasq Installation Script for CentOS
DNSmasq is a lightweight and convenient tool for configuring DNS and DHCP, suitable for small networks. It provides DNS functionality with optional DHCP capabilities. In the article Linux Install DNSmasq to Build Your Own Public DNS, the manual configuration method was shared. Since some users are not familiar with Linux, xiaoz has written a one-click script.
Applicable Environment
CentOS 6.x 7.x
Script Features
- One-click installation, ready to use with zero configuration
- Automatically allows TCP/UDP ports
- Enables access to Google and Facebook (scientific internet access)
- Scheduled updates for hosts lists
Installation
Copy the commands below for installation, one per line.
wget https://raw.githubusercontent.com/helloxz/dnsmasq/master/dns.sh --no-check-certificate
chmod +x dns.sh
./dns.sh
Usage
Refer to the Windows 7 DNS Setup Tutorial to change your DNS settings to your server's IP address.
Common Issues
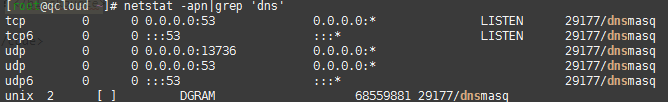
How to check if DNSmasq has started normally?
Enter the command netstat -apn|grep 'dns'. If you see the following screenshot, it indicates that the service has started normally.
Configured DNS but cannot access the internet, error: DNS not found?
Case 1: Check if the server supports security group features. Ensure that TCP/UDP port 53 is allowed in the security group.
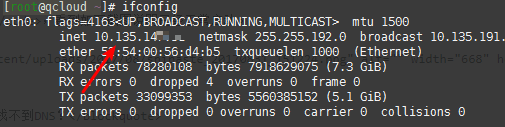
Case 2: If using a Tencent Cloud server, the script retrieves the public IP. You need to modify the /etc/dnsmasq.conf configuration file, changing listen-address= to your private IP, as shown in the screenshot below.
If you encounter other issues, please leave a comment below for feedback.
Other Notes
It is recommended to use a domestic server for setup; otherwise, resolution speeds will be very slow. If you wish to implement ad-blocking features, you will need to modify the configuration rules yourself.
Source Code: https://github.com/helloxz/dnsmasq
Supplement
New Normal: On September 19th, the blockade was upgraded. YouTube and Facebook have been added to the special care list, treated the same as *.twitter.com. If using official IPs (IPv4), once the firewall detects the CA certificate of the relevant domain, communication with the corresponding IP will be 100% intercepted and cut off. If using SNI server IPs to proxy some domains, they will also be intercepted, though not all IPs are blocked; usable IPs are very few. Interception only occurs on the exit route. In the near future, comprehensive deployment of CA certificate interception and other technologies will make hosts obsolete!!