WordPress Stored XSS Vulnerability Affects Versions 4.2 and Below
A few days ago, Aliyun Shield detected an XSS vulnerability on a website. Initially, it was not taken seriously, but later articles confirmed the issue. Checking WordPress's update records confirmed the existence of this vulnerability. It is recommended that site administrators upgrade to the latest version.

WordPress officially released version 4.1.2 on April 21, mentioning the fix of a severe stored XSS vulnerability. Shortly after, details of the vulnerability were revealed. The security research team Klikki Oy discovered that the vulnerability could still be exploited in the new version (<=4.2) of WordPress.
XSS Vulnerability 1
This XSS vulnerability occurs in the WordPress comment section, caused by a MySQL feature. In the MySQL utf8 character set, a character consists of 1 to 3 bytes. For characters larger than 3 bytes, MySQL uses the utf8mb4 format for storage. If a utf8mb4 character is inserted into a column encoded with utf8, MySQL in non-strict mode will truncate the subsequent content.
Vulnerability Details: Leveraging this feature, the author discovered this WordPress XSS vulnerability. WordPress defaults to utf8 encoding and does not have strict mode enabled. If we add a comment like this:
<abbr title='WeThis causes the WordPress page layout to become chaotic. If another comment is inserted, it creates an XSS vulnerability:
cedric' onmouseover='alert(1)' style='position:fixed;top:0;left:0;width:100%;height:100%'The page will display as follows:

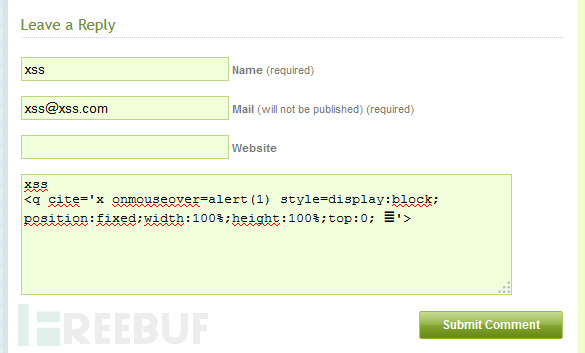
The author provided a Proof of Concept (POC):
sometext
<blockquote cite='x onmouseover=alert(1)
Affected Versions: WordPress 4.1.1 and earlier versions are affected. It is reported that version 4.1.2 has fixed this vulnerability.
XSS Vulnerability 2
Shortly before, the security research team Klikki Oy discovered that the vulnerability could still be exploited in newer versions of WordPress. The principle is the same, utilizing truncation to cause page layout chaos. However, this time Klikki Oy exploited another MySQL feature.
In the WordPress wp_comments table, the column storing comments is comment_content, with a type of text. Text can store up to 64KB of data. If a user inputs data larger than 64KB, MySQL will truncate the subsequent content. Since WordPress does not limit the length of comment content, submitting a comment larger than 64KB can still cause page layout chaos, forming an XSS vulnerability.
Below is the POC provided by the Klikki Oy team:
<a title='x onmouseover=alert(unescape(/hello%20world/.source))
style=position:absolute;left:0;top:0;width:5000px;height:5000px
AAAAAAAAAAAA [64 kb] ...'></a>
Affected Versions: WordPress 4.2 and below versions are affected.
Note: I am not very knowledgeable about security. This vulnerability mainly targets comments. It is recommended that site administrators upgrade WordPress to the latest version, or refer to How to Effectively Stop WordPress Spam Comments to effectively stop non-Chinese comments. Original source: WordPress Stored XSS Vulnerability Affects Versions 4.2 and Below