Nginx HTTP/2 and HTTPS Performance Test
HTTP/2 is the next-generation HTTP protocol developed by the Internet Engineering Task Force. For detailed information, please refer to the HTTP/2 introduction.

If you have not yet enabled HTTPS, please refer to the article: Nginx Force HTTPS, HTTP 301 Redirect to HTTPS. Enabling HTTP/2 support in Nginx is very simple; you only need to change listen 443; to listen 443 ssl http2;. Don't forget to reload Nginx.
HTTP/2 Test
How to know if your website supports HTTP/2 after enabling it? You can install the HTTP/2 and SPDY indicator extension in Chrome or Firefox browsers. If the website supports HTTP/2, it will automatically display in blue; if it is gray, it means it is not supported. Additionally, Chrome 51 and later require ALPN support, otherwise it will downgrade to HTTP/1.1.
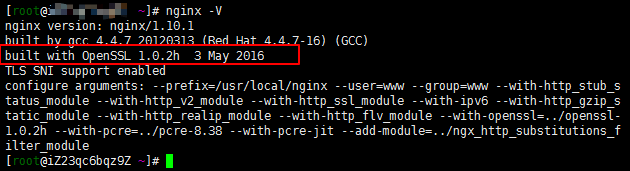
OpenSSL Version
ALPN requires support from OpenSSL 1.0.2. Currently, the latest version of OneinStack supports OpenSSL 1.0.2. You can check this by entering nginx -V.
Nginx HTTPS Optimization
On V2, a netizen shared configuration rules that resulted in a significant improvement in benchmark scores after testing. You can use the following rules directly:
ssl_protocols TLSv1 TLSv1.1 TLSv1.2; # Allowed protocols
ssl_ciphers EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5; # Encryption algorithms (CloudFlare recommended cipher suite)
ssl_prefer_server_ciphers on; # Optimize SSL cipher suite
ssl_session_timeout 10m; # Client session cache time
ssl_session_cache builtin:1000 shared:SSL:10m; # SSL session cache type and size
ssl_buffer_size 1400; # 1400 bytes to fit in one MTU
add_header Strict-Transport-Security max-age=15768000;
ssl_stapling on;
ssl_stapling_verify on;
Below is the complete rule set for XiaoZ's blog for reference:
server {
listen 443 ssl http2;
ssl_certificate /data/ssl/xiaoz.me.crt;
ssl_certificate_key /data/ssl/xiaoz.me.key;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2; # Allowed protocols
ssl_ciphers EECDH+CHACHA20:EECDH+AES128:RSA+AES128:EECDH+AES256:RSA+AES256:EECDH+3DES:RSA+3DES:!MD5; # Encryption algorithms (CloudFlare recommended cipher suite)
ssl_prefer_server_ciphers on; # Optimize SSL cipher suite
ssl_session_timeout 10m; # Client session cache time
ssl_session_cache builtin:1000 shared:SSL:10m; # SSL session cache type and size
ssl_buffer_size 1400; # 1400 bytes to fit in one MTU
add_header Strict-Transport-Security max-age=15768000;
ssl_stapling on;
ssl_stapling_verify on;
server_name xiaoz.me www.xiaoz.me;
index index.html index.htm index.php;
include /usr/local/nginx/conf/rewrite/wordpress.conf;
root /data/wwwroot/xiaoz.me;
location ~ [^/].php(/|$) {
#fastcgi_pass remote_php_ip:9000;
fastcgi_pass unix:/dev/shm/php-cgi.sock;
fastcgi_index index.php;
include fastcgi.conf;
}
location ~ .*\.(gif|jpg|jpeg|png|bmp|swf|flv|ico)$ {
expires 30d;
access_log off;
}
location ~ .*\.(js|css)?$ {
expires 7d;
access_log off;
}
}
server {
listen 80;
server_name xiaoz.me www.xiaoz.me;
rewrite ^(.*) https://blog.xiaoz.org$1 permanent;
}
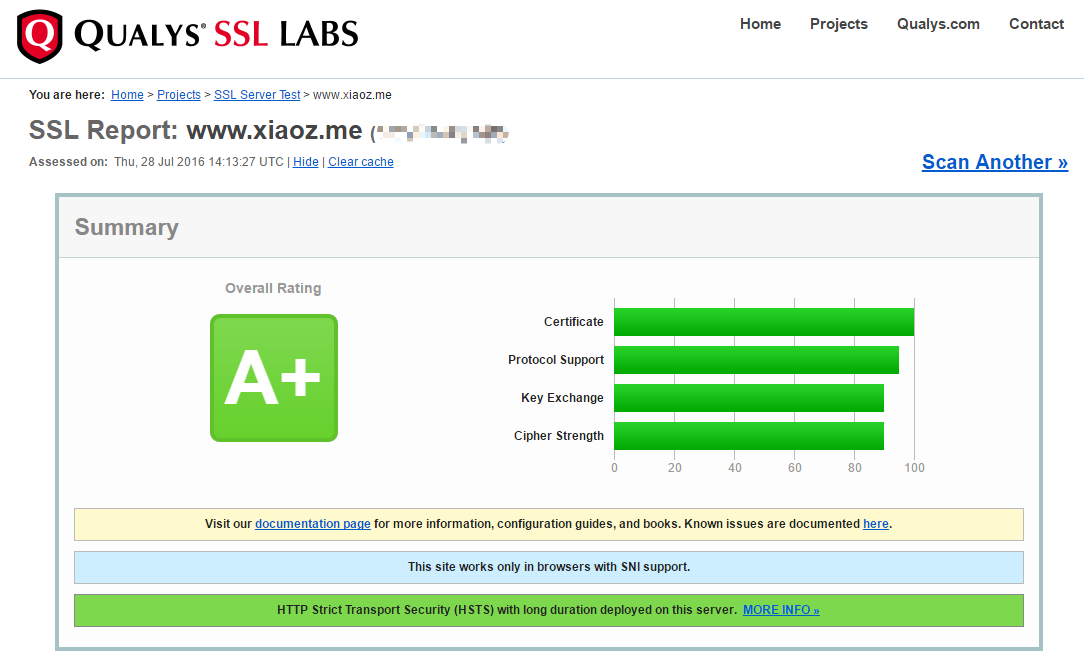
HTTPS Benchmark Test
You can open SSL LABS to test your website's HTTPS benchmark score. If you have upgraded to OpenSSL 1.0.2 and enabled HTTP/2, the benchmark score will show a significant improvement. Below are comparison screenshots from XiaoZ's blog:

Summary
If you enjoy tinkering, consider upgrading OpenSSL to 1.0.2, and please back up important configurations. Additionally, UpYun CDN also supports HTTP/2. If you do not want to tinker, you can directly use UpYun CDN, provided you have a BA account.
This article references: Why should we support ALPN as soon as possible? About Nginx enabling HTTP/2 issues