How to Apply for ZeroSSL Wildcard SSL Certificates Using acme.sh
In an earlier article, we shared how to use the acme.sh script to apply for Let's Encrypt wildcard SSL certificates. With continuous updates from the acme.sh author, the tool has become increasingly powerful and now supports multiple certificate providers including ZeroSSL, BuyPass, and Let's Encrypt.

It is rumored that the Let's Encrypt OSCP server is blocked in China, causing slow loading speeds for the first visit to sites using Let's Encrypt SSL. It is currently unclear if this has been resolved (some say Let's Encrypt has changed its OSCP server, but xiaoz has not verified this). Regardless, having more options is always better. This article shares another SSL service provider: ZeroSSL.
About ZeroSSL
ZeroSSL was launched in 2016. Like Let's Encrypt, its certificates are valid for only 90 days and support wildcard SSL certificates. Unlike Let's Encrypt, ZeroSSL's API has no rate limits, so there is no issue with being restricted when applying for SSL certificates multiple times from the same IP. ZeroSSL also provides a web interface for managing SSL certificates in the background, offering richer functionality compared to Let's Encrypt.
According to the acme.sh documentation, the default server is Let's Encrypt. Version 3, scheduled for release on August 1, 2021, will change the default server to ZeroSSL (Reference: https://github.com/acmesh-official/acme.sh/wiki/Change-default-CA-to-ZeroSSL). This indicates that ZeroSSL is becoming increasingly popular, and acme.sh is aligning with it.
Installing acme.sh
acme.sh implements the ACME protocol, helping you quickly apply for SSL certificates and automatically update them, greatly simplifying the operation steps. Before using it, we need to install it. The following commands are completed on a Linux system.
# Install acme.sh
curl https://get.acme.sh | sh
Yes, it only takes a simple one-line command to install. After installation, you can enter acme.sh -v to check the current version.
[root@qcloud-cd ~]# acme.sh -v
https://github.com/acmesh-official/acme.sh
v2.9.0
Changing the acme.sh Server to ZeroSSL
acme.sh version 2.x defaults to using Let's Encrypt as the service provider. We can change it to ZeroSSL using the following command:
# Change default provider to ZeroSSL
acme.sh --set-default-ca --server zerossl
Configuring DNS API
SSL certificate verification can be done via DNS validation, file validation, and other methods. To facilitate applying for multiple domains and subsequent certificate updates, the DNS API method is recommended. However, settings must be configured before use.
If using DNSPod (Domestic Version), the command is:
export DP_Id="1234"
export DP_Key="sADDsdasdgdsf"
The key can be obtained from: https://console.dnspod.cn/account/token/apikey.
If using Huawei Cloud Resolution (Domestic Version), the command is:
export HUAWEICLOUD_Username=<Your Username> # Usually hwxxxxxx
export HUAWEICLOUD_Password=<Your Password>
export HUAWEICLOUD_ProjectID=<A Project ID>
- HUAWEICLOUD_Username: Huawei Cloud username
- HUAWEICLOUD_Password: Huawei Cloud password
- HUAWEICLOUD_ProjectID: Can be obtained from My Credentials
acme.sh supports multiple DNS service providers. We will not list them all here; you can check the settings via the official documentation: https://github.com/acmesh-official/acme.sh/wiki/dnsapi.
ZeroSSL Usage Instructions
Before applying for a certificate, it is recommended to register an account on the ZeroSSL official website: https://zerossl.com/ to facilitate binding and associating certificates applied via acme.sh.
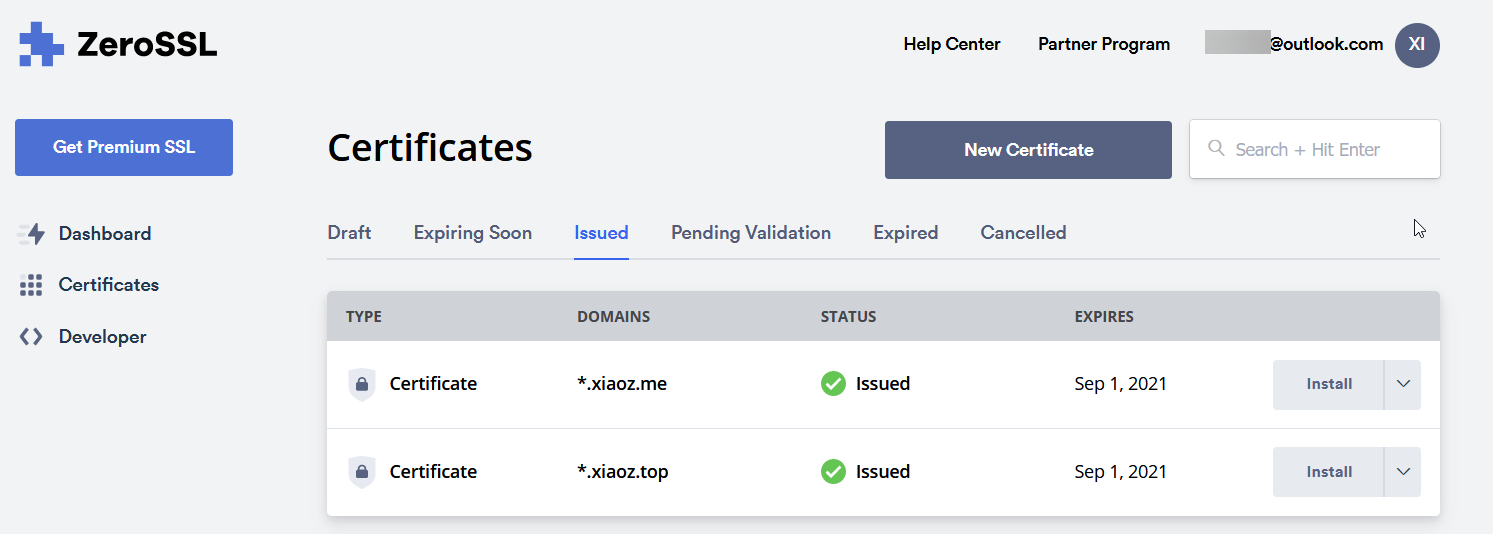
Also note that if you apply for an SSL certificate online through the ZeroSSL official website, free accounts are limited to 3 domains. However, there is no such limit when applying via acme.sh, so it is recommended to use acme.sh for application as it is simple and convenient.
Applying for ZeroSSL Wildcard SSL Certificates with acme.sh
If using for the first time, you need to register a ZeroSSL account (refer to the previous step). If already registered, the following command will automatically associate the account:
acme.sh --register-account -m myemail@example.com --server zerossl
(Note: Change myemail@example.com to your own ZeroSSL email address; do not fill it randomly.)
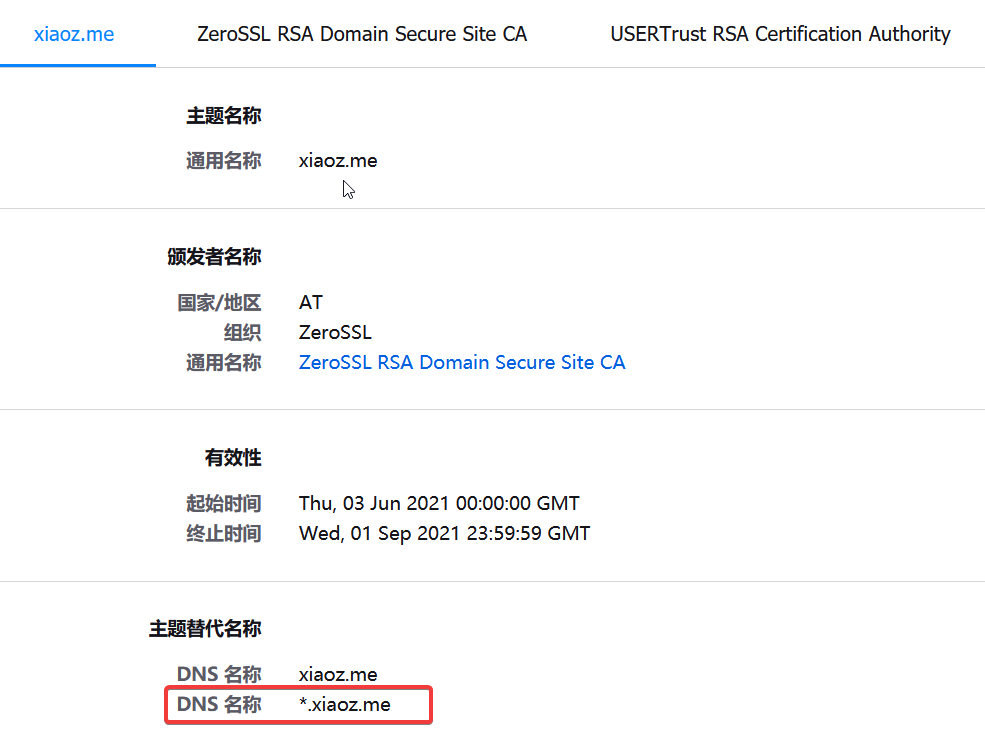
Taking the xiaoz.me domain as an example, which uses Huawei Cloud resolution, and assuming the Huawei Cloud DNS API has been set up in the previous step, you can now enter the command directly to apply:
# Apply for ZeroSSL wildcard SSL certificate
acme.sh --dns dns_huaweicloud --issue -d xiaoz.me -d *.xiaoz.me
If there are no errors during the application process, you can copy the SSL certificate to any desired location for use using the following command:
acme.sh --installcert -d xiaoz.me \
--key-file /data/ssl/xiaoz.me.key \
--fullchain-file /data/ssl/xiaoz.me.crt
The above command exports the xiaoz.me SSL certificate to the /data/ssl directory.
Deployment and Verification
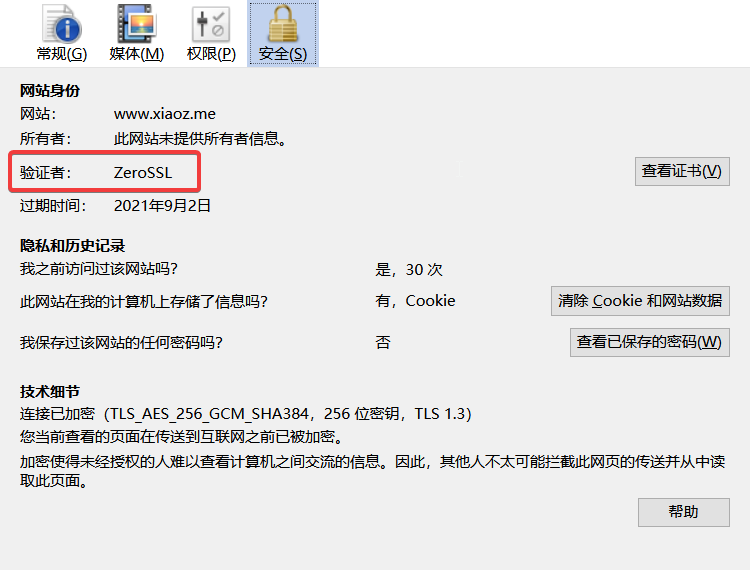
This article does not cover how to deploy SSL certificates; it is recommended to search online. After deployment, you can view the certificate information via a browser, as shown in the figures below.
Conclusion
ZeroSSL inherits almost all features of Let's Encrypt and also supports web management of certificates. Using acme.sh to apply for ZeroSSL is also very simple, making it a perfect alternative to Let's Encrypt. Unfortunately, like Let's Encrypt, the free version of SSL certificates is valid for only 90 days. However, having an additional SSL service provider choice is excellent. Why not give it a try?
- ZeroSSL Official Website: https://zerossl.com/
acme.shProject Address: https://github.com/acmesh-official/acme.sh