How to Apply for Let's Encrypt Wildcard SSL Certificates Using acme.sh
Let's Encrypt is a certificate authority launched in 2015 that has always provided free SSL certificate services. Today, the long-awaited Let's Encrypt wildcard SSL certificate is here, and you can easily apply for it using acme.sh.
acme.sh implements the ACME protocol and is an open-source tool for applying for Let's Encrypt SSL certificates. Its operation and process are much simpler than the official application method, so it is recommended for use.
Install acme.sh
Run the following commands on a Linux system. Both root and ordinary users can install it.
# Install
curl https://get.acme.sh | sh
# Make alias effective
source ~/.bashrc
Configure DNS API
Currently, wildcard certificates only support DNS verification. acme.sh automatically completes the operation through the DNS provider's API, so you need to configure the DNS API first. Taking CloudXNS as an example:
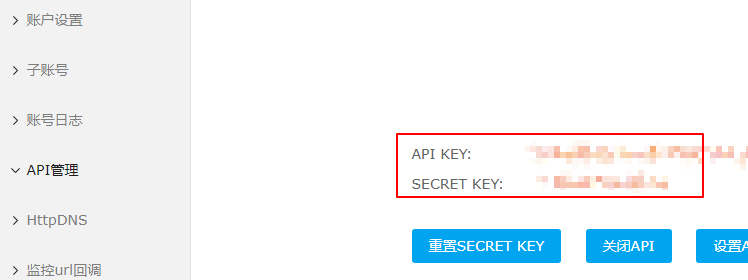
In the CloudXNS backend - User Center - API Management, you can see the API KEY/SECRET KEY. If you don't have one, please create it and record it.
Run the following command to import the key (CloudXNS). Note that different DNS providers require different import parameters. For details, please refer to: dnsapi
export CX_Key="1234"
export CX_Secret="sADDsdasdgdsf"
CX_Key: Corresponds to the CloudXNS API KEYCX_Secret: Corresponds to the CloudXNS SECRET KEY
Other Common DNS API Configurations
CloudFlare
# Import key
export CF_Key="sdfsdfsdfljlbjkljlkjsdfoiwje"
export CF_Email="xxxx@sss.com"
# Apply for certificate
acme.sh --issue --dns dns_cf -d example.com -d www.example.com
Tencent/DNSPod (Domestic Version)
# Import key
export DP_Id="1234"
export DP_Key="sADDsdasdgdsf"
# Apply for certificate
acme.sh --issue --dns dns_dp -d example.com -d www.example.com
Alibaba Cloud
# Import key
export Ali_Key="sdfsdfsdfljlbjkljlkjsdfoiwje"
export Ali_Secret="jlsdflanljkljlfdsaklkjflsa"
# Apply for certificate
acme.sh --issue --dns dns_ali -d example.com -d www.example.com
For more DNS API configurations, please refer to: https://github.com/Neilpang/acme.sh/tree/master/dnsapi
Issue Wildcard Certificate
Taking CloudXNS DNS as an example, we will issue a wildcard certificate for awk.sh.
acme.sh --issue --dns dns_cx -d awk.sh -d *.awk.sh
After a successful application, you will be prompted with the absolute path of the certificate (as shown in the screenshot below). You can then deploy the SSL certificate on your web server.
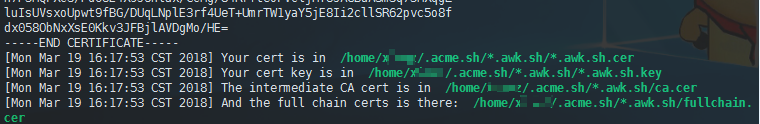
If you are using Nginx, refer to How to Deploy SSL Certificates with Nginx to deploy the SSL certificate. Generally, you will only need the fullchain.cer and domain.com.key files.
Copy Certificate
After the certificate is generated, you need to copy it to the location where it is actually needed. The generated certificates are stored in the installation directory: ~/.acme.sh/. Please do not use the files in this directory directly. The correct method is to use the --installcert command and specify the target location. The certificate files will then be copied to the corresponding location. For example:
acme.sh --installcert -d xiaoz.top \
--key-file /data/ssl/xiaoz.top.key \
--fullchain-file /data/ssl/xiaoz.top.cer \
--reloadcmd "service nginx force-reload"
Summary
Currently, Let's Encrypt supports multi-domain and wildcard certificates, but the disadvantage is that the validity period is still only three months. Even if you can set up a script for automatic renewal, management and maintenance can still be somewhat inconvenient.
Some content is referenced from: https://github.com/Neilpang/acme.sh