Preventing DDoS Attacks on WordPress via Pingback
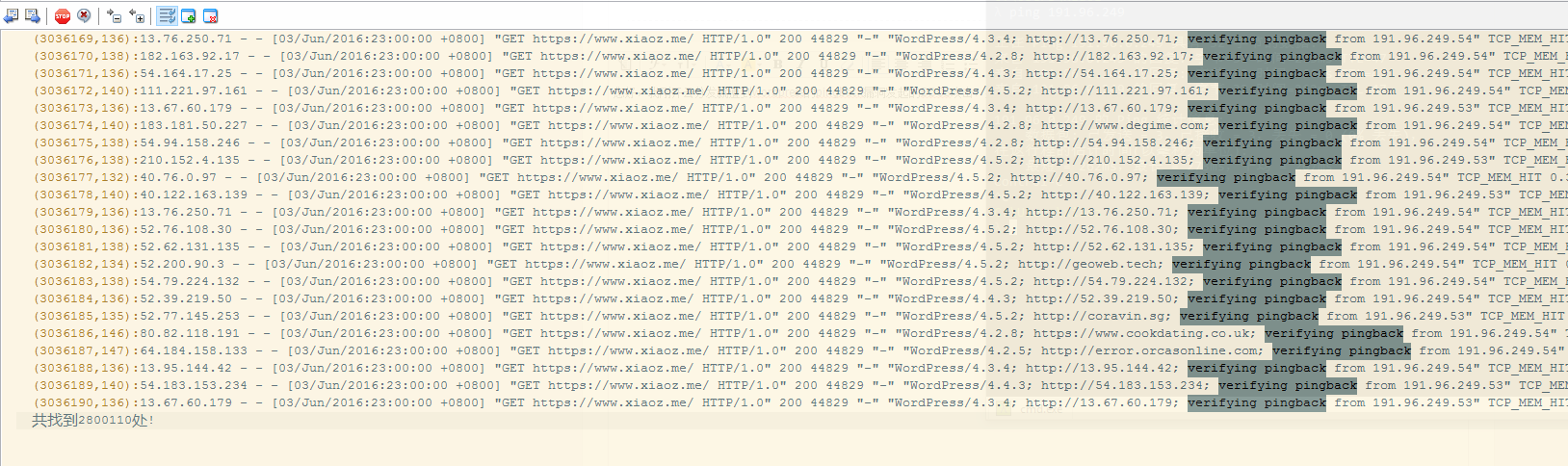
Two days ago, my blog server was hit by a DDoS attack. Initially, the attacker used SYN attacks on port 443, exhausting Nginx resources and saturating the bandwidth. Redirecting traffic abroad proved ineffective, forcing me to shut down the server. After waves of attacks, the attacker switched tactics, utilizing WordPress pingbacks to launch a DDoS attack, rendering the website inaccessible.
Disable Pingback Functionality
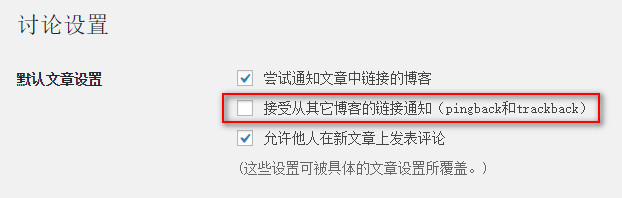
Pingback, translated as "citation" in Simplified Chinese WordPress, essentially notifies the other party that something related to them has occurred. Since this feature is rarely used, it is best to disable it directly. Go to Dashboard > Settings > Discussion and uncheck the option Allow link notifications from other blogs (pingbacks and trackbacks), then save the changes.
Modify Nginx Configuration
If you are using Nginx as your web server, add the following code to your host configuration file, typically located at /usr/local/nginx/conf/vhost/youdomain.conf. Insert it within the server block, and then reload Nginx using service nginx reload.
if ($http_user_agent ~* "WordPress") {
return 403;
}
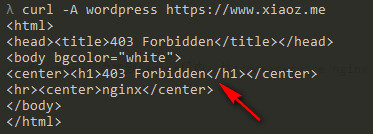
Test with CURL
You can use CURL to simulate a request and verify if the configuration is effective. If a 403 error is returned, the configuration is successful.
Additional Content
Although blocking WordPress user agents in Nginx results in a 403 error, it still generates a large number of requests that consume server resources. To address this, add the following code to your theme's functions.php file:
add_filter( 'xmlrpc_methods', function( $methods ) {
unset( $methods['pingback.ping'] );
return $methods;
} );
Other Notes
If your website uses a third-party CDN service, you can prevent WordPress pingback attacks by adding WordPress user-agent requests to the blacklist. For more details, please refer to this article on Wooyun (now known as FreeBuf): Over 160,000 WordPress Sites Used for DDoS Attacks.